
The descibed things in that article are nothing new, but there are still lot of devices around which have WPS enabled!
I’ll split this tutorial in two parts. Part 1 is to get a basic understanding what WPS is and how the weakness works. In part 2 I’ll show you step by step how you can simulate a WPS attack with Kali Linux.
- WPS – (In)Security P1
- WPS – (In)Security P2
WPS stands for WI-FI Protected Setup and it is a networking standard that tries to make connections between a router and wireless devices easier and faster. Instead of entering the WP2-PSK key for each device you can use WPS to connect your devices to the network.
There are several ways to connect to a wireless network that uses WPS:
- First, press the WPS button on your router to turn on the discovery of new devices. Then, go to your laptop, tablet or smartphone and select the network you want to connect to. Your device gets automatically connected to the wireless network without entering the network password.
- You may have devices like wireless printers or wireless range extenders with their own WPS button that you can use for making very quick connections. Connect them to your wireless network by pressing the WPS button on the router and then on those devices. You don’t have to input any data during this process. WPS automatically sends the network password and these devices remember it for future use. They will be able to connect to the same network in the future without you having to use the WPS button again.
- A third method involves the use of an eight-digit PIN. All routers with WPS enabled have a PIN code that’s automatically generated and it cannot be changed by users. You can learn this PIN from the WPS configuration page on your router. Some devices without a WPS button but with WPS support will ask for that PIN. If you enter it, they authenticate themselves and connect to the wireless network.

The first two points seems to be more or less secure, because you’ve to press the WPS button on the router that make it difficult for a remote attacker if he has no physical access. But what’s about the third method with the 8 digit pin?

Bruteforece a 8 digit pin = 10^8 = 100’000’000 possibilities! Sounds secure, but…
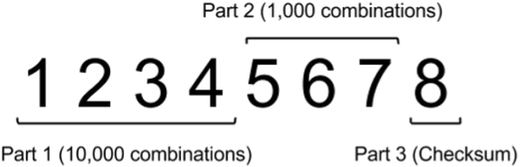
Back in 2011, a security researcher discoverd that you don’t need to try all 100’000’000 pin combinations. The last digit is just a check digit that is calculated from the previous seven. That means that WPS pins are effectively only seven digits long.
But not enough, the 8-step protocol doesn’t validate the pin in form of a seven digit number. It checks the first four digits and only if those are right it does check the last three digits.
10^4 = 10’000 + 10^3 = 1’000. Instead of 10’000’000 combinations you only have to try 11’000 combinations to get the WP2-PSK key.
The problem is known since 2011, but most of the vendors who implement WPS functionality in their devices didn’t react. Such an attack can still be lucrative for an attacker, because WPS is activated by default in most devices and it won’t by hard to find WPS routers in your environment if you do a scan. Another fact is that not many routers have implemented security meassures against a WPS bruteforece attack, forexample that your MAC Address will be locked out after few false tries…
Let’s move over to part 2 where I’ll show you step by step how you can do such a attack 🙂

Schreib einen Kommentar